In the complex world of industrial systems, security is a crucial priority. Have you ever considered the potential vulnerabilities that could compromise the robustness of your infrastructure? That’s what we’re going to look at in this blog post. But first, imagine:
“An electronics manufacturing plant. Everything seems to be running smoothly until an operator notices an unusual alert on the SCADA system. Unbeknownst to him, malicious software has entered the network via a machine connected to the IT network. Within a few hours, the PLCs slowed down production, causing defects in finished products. After investigation, the origin of the problem was identified: an uncorrected flaw in a firewall, which could have been detected during a pentest.
I. Introduction to pentesting and its application in industry
Imagine a cybersecurity expert deploying a battery of sophisticated tests to put your system’s resilience to the test. This is exactly where pentesting comes in, essential for identifying and neutralizing vulnerabilities that could jeopardize your industrial IS. Let’s dive into the fascinating world of pentesting, in the depths of your industrial IT system.

Cybersecurity in industrial networks
When it comes to industrial system security, it’s essential to understand that these environments present unique specificities compared to traditional networks. Industrial networks are more difficult to protect, not least because of the many operating constraints that make upgrades very difficult. What’s more, the priority in industrial networks is not data confidentiality, but machine availability, adding yet another hurdle to cybersecurity.
The consequences of a successful attack can be devastating, ranging from loss of production to major property damage, and even risks to employee safety. What’s more, companies are increasingly dependent on their IT infrastructures to ensure their day-to-day operations and competitiveness in the marketplace. However, this increased dependence also exposes them to a growing risk of cyber-attacks.
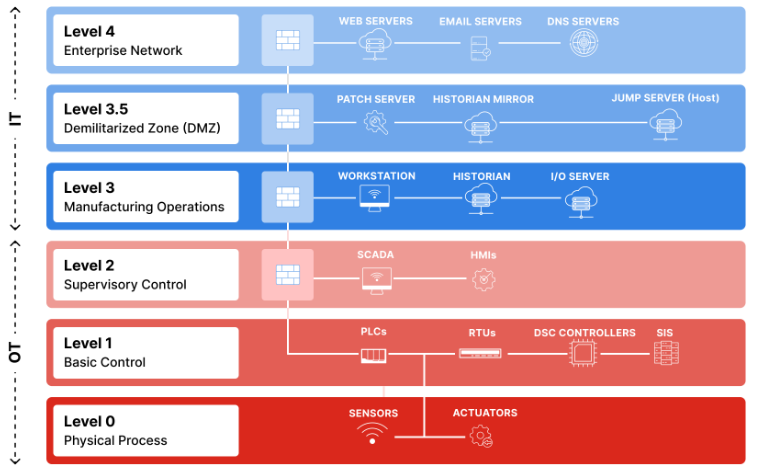
The specifics of industrial pentesting – The Purdue model
The Purdue model [ExternalLink] is an architecture commonly used in industrial environments to segment networks into three main levels:
- IT level (Enterprise) – Levels 4 & 5: Administrative management.
- OT level (Workshops) – Levels 3 & 2/3: Supervision and control systems.
- ICS level (Industrial Control) – Levels 1 & 2: PLCs and critical equipment.
Pentesting in an industrial environment aims to identify potential vulnerabilities that could be exploited by malicious attackers. This mainly involves assessing the industrial network’s resistance to external intrusion attempts.
It is therefore essential to understand how an attacker could attempt to access the industrial network from the IT network or from outside the company, and what security measures are in place to prevent this.
The vulnerabilities that may be identified may be technical in nature, such as software or hardware vulnerabilities, or they may result from human error, such as weak passwords or incorrect network configuration.
II. Pentest methodology for industrial information systems
Industrial IS pentesting generally follows a well-defined methodology to guarantee accurate and reliable results. This methodology includes several key steps:
- Information gathering: experts gather information on the target industrial system, including its architecture, hardware and software components, and communication protocols.
- Vulnerability analysis: experts analyze the various potential vulnerabilities of the industrial system using specialized tools and advanced techniques.
- Exploiting vulnerabilities: once vulnerabilities have been identified, experts attempt to exploit them to gain access to the industrial system or its sensitive data. As industrial systems are very fragile, this stage is not always carried out within the system itself, but in other networks of the target organization.
- Report and recommendations: at the end of the pentest, a detailed report is usually provided, highlighting the vulnerabilities identified, the associated risks and recommendations for strengthening system security.
Pentest methodologies specific to industrial systems
Here are the steps we take to ensure reliable results. As mentioned earlier, these industrial systems are very sensitive, and we have to be very careful. Here’s our methodology at Hackmosphere:
- Industrial organizational audit: to identify weaknesses in the industrial network as a whole, in particular the identification of dual-member machines (with access to the OT and IT network) and the architecture in place compared with the Purdue model.
- Review of firewall configuration: to check flows authorized to enter or leave the industrial network
- Pentest IT: aimed at taking control of firewalls or dual-homed machines
- Pentest OT: Once all the other points have been dealt with, we try to move forward very carefully and in close collaboration with the customer.
Examples of vulnerabilities in the industrial network
A pentest based on this model evaluates security at each level and the interactions between them. Here’s how it can help identify certain vulnerabilities:
- IT/OT convergence: The growing interconnection between IT (traditional networks) and OT (industrial systems) exposes industrial systems to threats from IT environments, such as ransomware or phishing.
- Unsecured protocols : Many industrial protocols (Modbus, DNP3, etc.) do not encrypt communications. A hacker can exploit this weakness to intercept or manipulate critical data, such as commands to PLCs.
- Uncontrolled access: Critical equipment (PLC, HMI) can sometimes be exposed at default interfaces (password “admin”) or via unused open ports, facilitating unauthorized access.
- Missing updates: Industrial systems are often old and unable to apply security patches, leaving known vulnerabilities open to exploitation.
- Insufficient access audits: Poorly configured user rights allow internal employees or attackers to modify sensitive systems.
A Purdue pentest brings these vulnerabilities to light, helping to define a robust security strategy, including segmentation, patch management and proactive monitoring.

A striking, real-life example of an attack on an industrial system is the “Stuxnet” virus. This malware, designed to sabotage centrifuges in Iranian nuclear facilities, exploited specific flaws in SCADA systems. It demonstrated how malware can infiltrate isolated networks via infected USB sticks and disrupt critical equipment. This attack underlines the crucial importance of pentests to detect such vulnerabilities before they are exploited.
III. Analysis of results and recommendations
Once the pentest has been completed, the results must be analyzed in detail to understand the flaws identified and assess their potential impact on the security of the industrial system as a whole. This analysis is also used to determine the corrective measures required to enhance system security. Recommendations arising from the analysis of the results may include actions such as updating software (if possible), modifying network configurations, strengthening passwords or adding new layers of security to protect the system against future attacks.
Best practices and tips for strengthening the security of industrial information systems (IS)
To strengthen the security of an industrial IS, it is essential to follow certain best practices and advice:
- As industrial networks are very difficult to protect, it is essential to provide the best possible protection for all systems with external access.
- Wherever possible, regularly update the software used in the industrial system to apply available security patches.
- Use strong, unique passwords for all industrial system accounts.
- Restrict physical access to industrial system equipment by implementing appropriate access controls.
- Implement continuous monitoring of the industrial system to quickly detect any suspicious activity or intrusion attempts
IV. Conclusion and outlook
In this article, we explored the fascinating world of pentesting in industrial systems. We have seen how this proactive assessment method can help identify vulnerabilities that could compromise the security of an industrial IS. By following the best practices and tips mentioned, you can strengthen the security of your industrial IS and protect your company against modern threats.
Industrial systems are increasingly being targeted by malicious attackers, making the protection of these infrastructures all the more crucial. By using specific methodologies and tools for industrial pentesting, you can assess your system’s resistance to attack, and take the necessary steps to enhance its security. By following the recommended best practices and advice, you can significantly reduce the risk of successful attacks against your industrial IS.
Would you like to test the security of your industrial IS? Contact Hackmosphere for a personalized audit and secure your critical infrastructures.