Blog
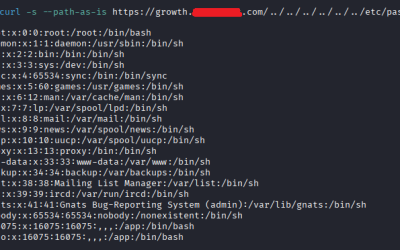
Pentest of a 100% vibe-encoded app: complete security analysis of an AI-generated app
Introduction: vibe coding meets cybersecurity The vibe coding is radically transforming the way applications are developed. Thanks to AI assistants and LLMs, it is now possible to generate a complete application - frontend, backend and API - simply by describing the...
What is an intrusion test?
Penetration testing is a proactive cybersecurity approach that involves simulating computer attacks to assess an information system's resistance to potential threats. Also known as pentesting, this allows you to put yourself in the shoes of a hacker by reproducing his...
How do you perform a penetration test for a web application?
Creating a penetration test for a web application is a complex process requiring technical skills, a rigorous methodology and in-depth knowledge of current IT threats. The process involves simulating real-life attacks on an online application to assess its resistance...
Bypassing Windows Defender antivirus in 2025: Evasion Techniques Using Direct Syscalls and XOR Encryption – Part 1
Reading Time: 10 minutesTechnical Level: Advanced Introduction As pentesters, we always have to keep up to date with the latest trends and of course, bypassing antiviruses is part of our activities. In this article, we will discuss how to bypass antiviruses and since...
In-store physical Pentest: feedback on a real case study
Cybersecurity is not limited to the digital sphere. Physical attacks are also part of the modus operandi used by cybercriminals. The principle is simple: look for a human or material flaw within your company to gain access to your data or disrupt the smooth running of...
Phishing campaign: Are decision-makers vulnerable?
Phishing: an underestimated threat Cybersecurity is a major issue for companies, and malicious phishing campaigns are among the most frequent threats. Yet corporate decision-makers, including CEOs and CTOs, are sometimes the...
How to obtain a time-based blind SQL injection and automate by modifying SQLMAP?
The cybersecurity of web applications is a crucial issue in a world where digital data has become a major asset. Among the most subtle threats, "time-based blind SQL injection" vulnerabilities stand out for their ability to exfiltrate data without triggering obvious...
Your security is important to us. What about you?
Take advantage of a free 30-minute functional audit to assess your current situation.